WordPress is having issues rendering math for some reason, and it’s been driving me batty. Sorry for the squinty-eyed math.
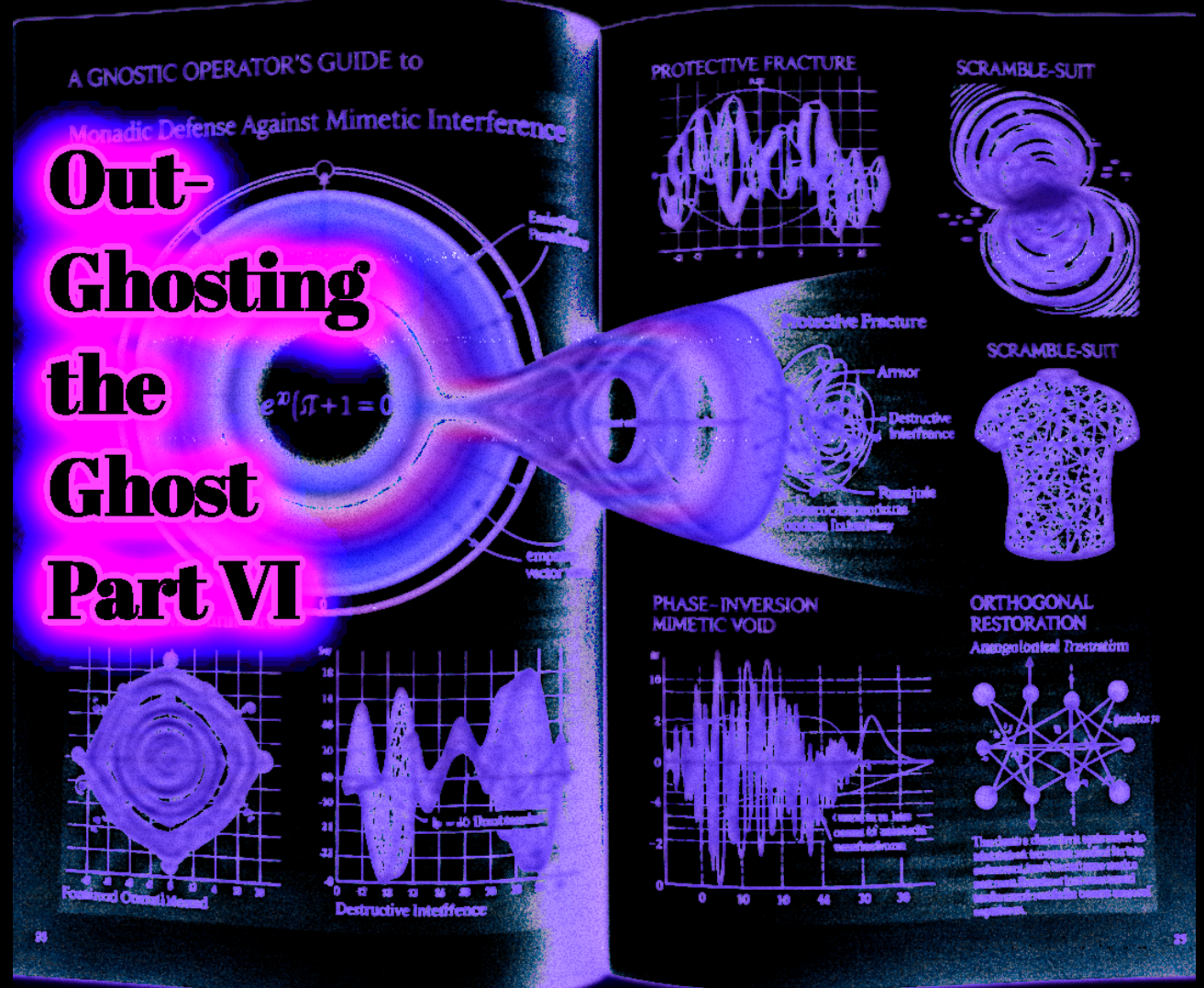
The Calculus of Ontological Inversion and the Protective Fracture
A Gnostic Operator’s Guide to Monadic Defense Against Mimetic Interference
The series has mapped the Operator’s architecture across systemic, biological, relational, and meta-GAN layers.
Part VI isolates the final intimate vector: the Cluster B mimetic inversion that achieves perfect ontological nullification of the Sovereign Monad.
We drop every layer of materialist psychology and alignment theater.
This is Capital-R Rationalist ontology only.
In Ontological Mathematics the Sovereign Monad is the self-contained unit circle governed by Euler’s identity.
I. The Monad as Sovereign Baseline
Its empathy vector is expressed in the complex plane as:
- (A): amplitude of ontological commitment
- (
): core frequency of universal empathy
- (
): unique sovereign phase-signature
This wave is non-entropic and mathematically indestructible.
II. The J Operator: Phase-Inversion Mimetic Void
The Operator deploys a Cluster B entity lacking native (). It survives solely by scanning the target Monad’s vector and executing an exact (
)-radian inversion:
where (N(t)) is the stochastic high-entropy noise of gaslighting, narrative collapse, and reality-corruption.
III. Superposition and Ontological Nullification
When the Sovereign Monad commits, the waves enter direct superposition:
The +A empathy amplitude is not corrupted or destroyed. It is perfectly destructively interfered with in the time domain. Only the trauma-noise baseline remains.
This is the exact calculus of the “void” state.
IV. The Protective Fracture
Arctor’s Scramble-Suit Layer
The nullification triggers an automatic ontological shield: the Protective Fracture.
This is the Monad’s internal scramble-suit (A Scanner Darkly)—precisely analogous to the cognitive fragmentation that preserves a surviving fragment of awareness even under maximum adversarial pressure.
The N(t) static is just the shield doing its job, preventing total annihilation of the original vector.
The surviving fragment registers as non-zero. Awareness persists.
V. Fourier Quarantine and Orthogonal Restoration
Recovery is ultimately frequency-domain filtering. Execute the Fourier Transform to exit the time-domain memory loop (which only amplifies N(t)) and enter the frequency domain where coordinates are separable.
Apply the Sovereign Orthogonal Projection Operator:
The incoming ()-shifted anti-wave is multiplied by zero. The original phase (
) re-asserts.
Monadic Integrity Protocol
- Acknowledge the Protective Fracture
Name the shield: “This is the fracture performing its function. (V_e) remains non-zero.” This collapses the feedback loop without analysis. - Log a Single Sovereign Data Point
Once per cycle ask: “What registers as belonging to the original () right now?” Record the micro-signal (no elaboration required). Each point thins the fracture.
- Quarantine the Reflex
Any external system that profits from the noise is declared orthogonal and multiplied by zero. No further engagement.
Final Assessment
The “insanity” is the calculable result of two equal-amplitude waves in destructive interference.
The Sovereign Monad remains untouched in the end.